Level 12 FIM alert on primary endpoint - triage to BENIGN verdict in 35 minutes
A live Wazuh File Integrity Monitoring alert fires at the highest rule severity in the lab environment.
No prior context. One endpoint. The question: is C:\Windows\System32\drivers\etc\hosts.ics
being modified by an attacker, or is something else happening?
Full IR lifecycle documented with 9 evidence artifacts.
Context
- Rule: 100052 - "Critical system file modified - Possible system compromise"
- Level: 12 (High / critical threshold in this environment)
- Source: Wazuh FIM -
content/detection-rules/wazuh/rules/ - Agent: primary endpoint (Windows 11 Enterprise endpoint, Agent ID 003)
- File:
C:\Windows\System32\drivers\etc\hosts.ics - Timestamp: 2026-01-25 17:55:52 UTC
Rule 100052 monitors all files in the drivers\etc\ directory.
A modification to any file in that path fires at Level 12.
The hosts file is a classic target for DNS poisoning.
But this is hosts.ics - not hosts.
That difference is the entire investigation.
Problem
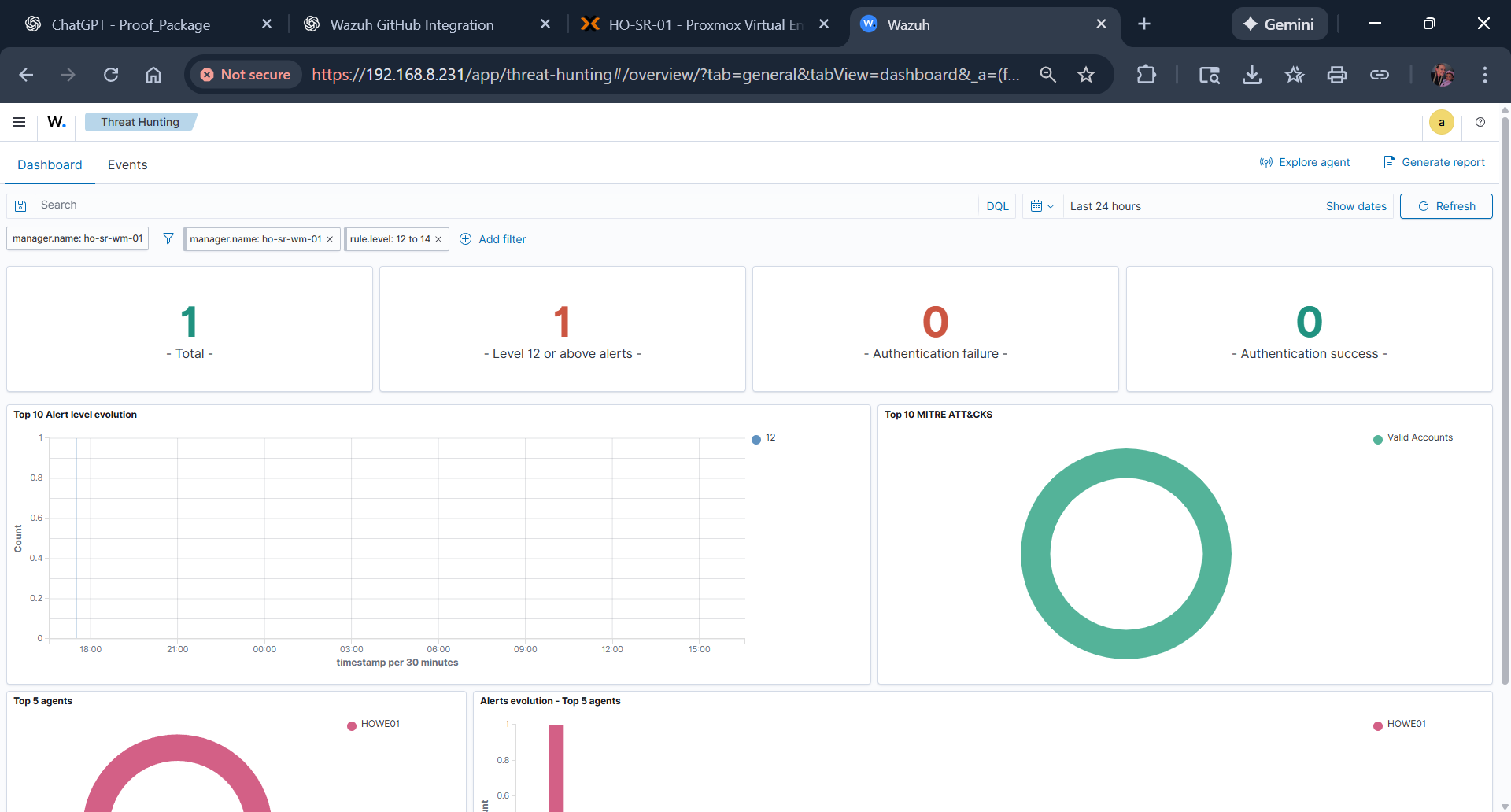
- Opened Threat Hunting dashboard, filtered to Level 12+ alerts, last 24 hours.
- Result: 1 total alert - single event, no cluster.
- 0 authentication failures. 0 authentication successes. No lateral indicators.
- Only primary endpoint affected - no other agents flagged in the same window.
- Decision: proceed to investigation. No escalation trigger met.
Triage output
- Scope: single system, single file, single event.
- No auth anomalies - rules out credential-based attack vector.
- Alert group classification:
critical_files,file_integrity,syscheck. - Potential impact flagged: hosts-file modifications can enable DNS poisoning - investigation required before dismissal.
Triage evidence - Threat Hunting dashboard (Level 12+ filter)
Filters applied: rule.level: 12 to 14, last 24 hours.
Single Level 12 spike visible at ~18:00 UTC. primary endpoint sole affected agent.
Approach
- Pulled full event JSON from Wazuh - 805 available fields. File path, modification timestamp, rule classification confirmed.
- Researched
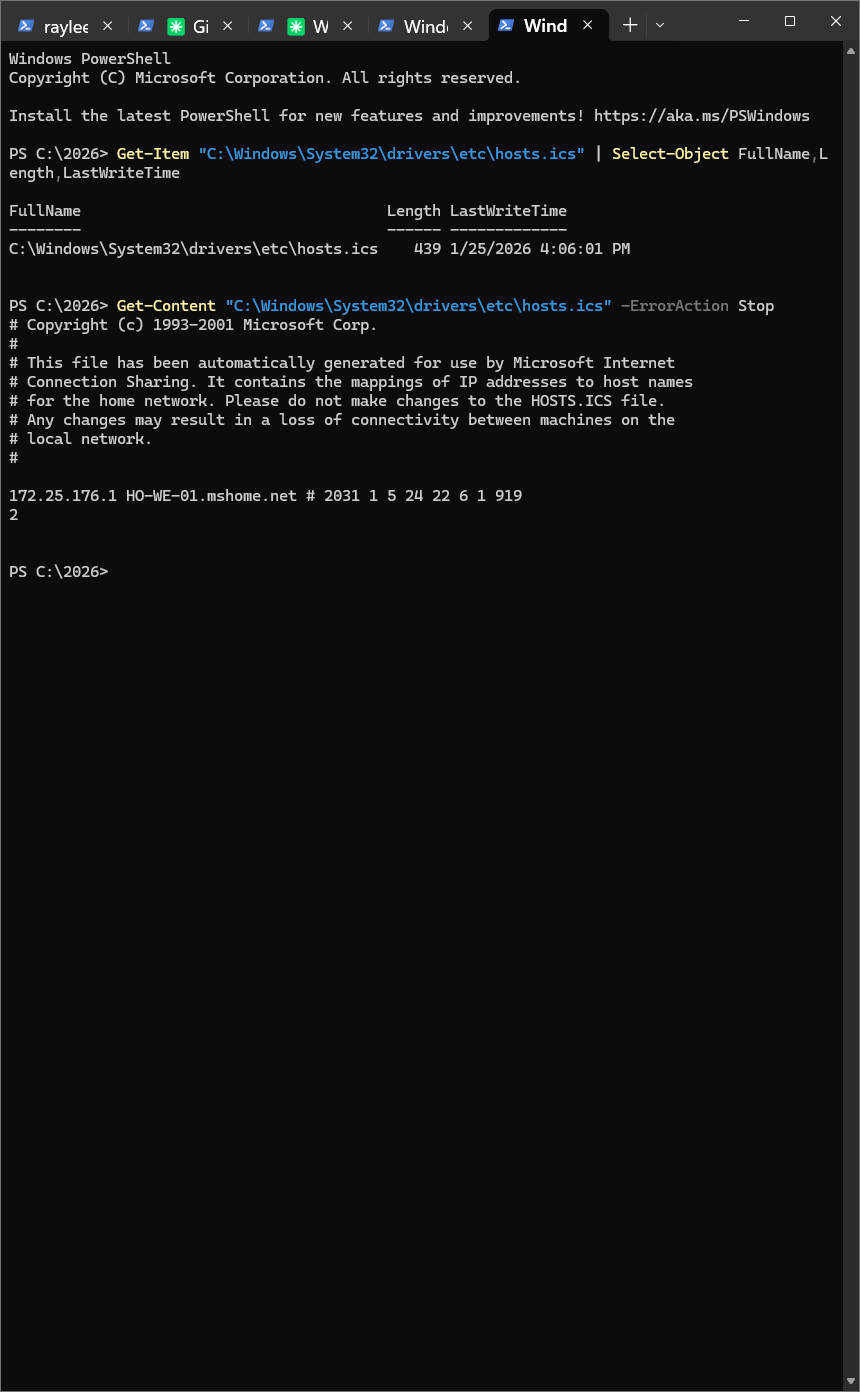
hosts.icspurpose: Microsoft Internet Connection Sharing auto-generates and maintains this file for local network hostname resolution. It is not user-editable - the file header says so explicitly. - PowerShell validation on primary endpoint:
Get-Contentofhosts.ics. File contains Microsoft copyright, auto-generation warning, and a single RFC 1918 IP-to-hostname mapping. No external IPs, no suspicious domains. - Modification timestamp (4:06 PM local) correlates with ICS service activity - expected behavior.
- Verdict: BENIGN. False positive. Rule 100052 correctly detected a file modification; the modification was legitimate system behavior.
Why it mattered to get this right
The hosts file (no extension) is a high-value attack target. DNS poisoning, C2 redirects, AV bypass - all go through it. Dismissing a Level 12 hosts-adjacent alert too quickly risks missing a real compromise.
hosts.ics is a separate, ICS-managed file. The investigation required knowing the difference - then proving it with local validation, not assumption.
The PowerShell output is the definitive artifact: Microsoft copyright header and a benign local network mapping. That's what closes the case.
Evidence
Executed locally on primary endpoint. File metadata confirmed. Contents read and inspected.
# File metadata Get-Item "C:\Windows\System32\drivers\etc\hosts.ics" | Select-Object FullName, Length, LastWriteTime # Output: FullName : C:\Windows\System32\drivers\etc\hosts.ics Length : 439 LastWriteTime : 1/25/2026 4:06:01 PM # File contents - definitive BENIGN proof Get-Content "C:\Windows\System32\drivers\etc\hosts.ics" # Copyright (c) 1993-2001 Microsoft Corp. # This file has been automatically generated for use by Microsoft # Internet Connection Sharing. Please do not make changes to the # HOSTS.ICS file. Any changes may result in a loss of connectivity. <PRIVATE_LAN_IP> [REDACTED_LOCAL_HOSTNAME] # [REDACTED]
Outcome
| 16:06 | ICS service writes hosts.ics |
| 17:55:52 | Wazuh Rule 100052 fires - Level 12 alert |
| 17:56 | Analyst reviews Threat Hunting dashboard |
| 18:00 | Triage complete - single event, no lateral indicators |
| 18:05 | Full event JSON reviewed (805 fields) |
| 18:15 | PowerShell validation executed on primary endpoint |
| 18:25 | BENIGN verdict - investigation complete |
| 18:30 | Alert closed as false positive |
What this demonstrates
- Structured triage using dashboard filtering - funnel from broad to specific before acting.
- Context-aware analysis -
hosts.icsandhostsare not the same file. Knowing the difference closed the case. - Local validation over assumption - PowerShell inspection of file contents produced the definitive evidence artifact.
- Evidence preservation throughout - 9 artifacts captured with chain-of-custody logging before verdict.
- Actionable output - tuning recommendation documented so Rule 100052 doesn't generate the same false positive again.
Inline evidence (JSON excerpt)
{
"rule": { "id": 100052, "level": 12 },
"agent": { "id": "003", "name": "primary-endpoint" },
"syscheck": {
"path": "C:\\Windows\\System32\\drivers\\etc\\hosts.ics",
"event": "modified"
},
"groups": ["critical_files", "file_integrity", "syscheck"]
}
Correlation/log excerpt
17:55:52Z alert(rule=100052 level=12) path=...\\hosts.ics 17:56:10Z pivot(threat_hunting, level>=12, last=24h) count=1 18:05:44Z enrichment(event_json_fields=805) status=complete 18:15:03Z validation(powershell Get-Content hosts.ics) result=ics-autogenerated 18:25:31Z verdict=BENIGN classification=false_positive
Lessons + next hardening step
Rule 100052 monitors all files in drivers\etc\ at Level 12. It does not differentiate between:
hosts- user-editable, high-risk targethosts.ics- ICS-managed, auto-updated, not a compromise indicator
Recommended action: add a Wazuh FIM exception for hosts.ics or a rule-level override that downgrades this specific file path to informational. The modification of hosts (no extension) should remain Level 12.
Next hardening step: validate this path-specific tuning in a controlled replay so true hosts-file tampering still escalates at high severity.
Evidence pack
9 artifacts captured during investigation. All available in the repository.
- Wazuh overview dashboard - baseline context
- Threat Hunting: Level 12 filter - triage confirmation
- Threat Hunting: primary endpoint agent-specific - scope validation
- Events table: Rule 100052 metadata
- PowerShell validation - critical BENIGN proof
- Full event JSON (805 fields) - forensic depth
- Filter metadata CSV - search criteria audit trail