PP_SOC_Integration: from a verified rule library to a live detection workflow
Evidence-first transition from static detection artifacts to a running SOC production-sim environment. Numbers are sourced from observed monitoring data; redacted screenshots and artifacts are available in the project repository.
Context
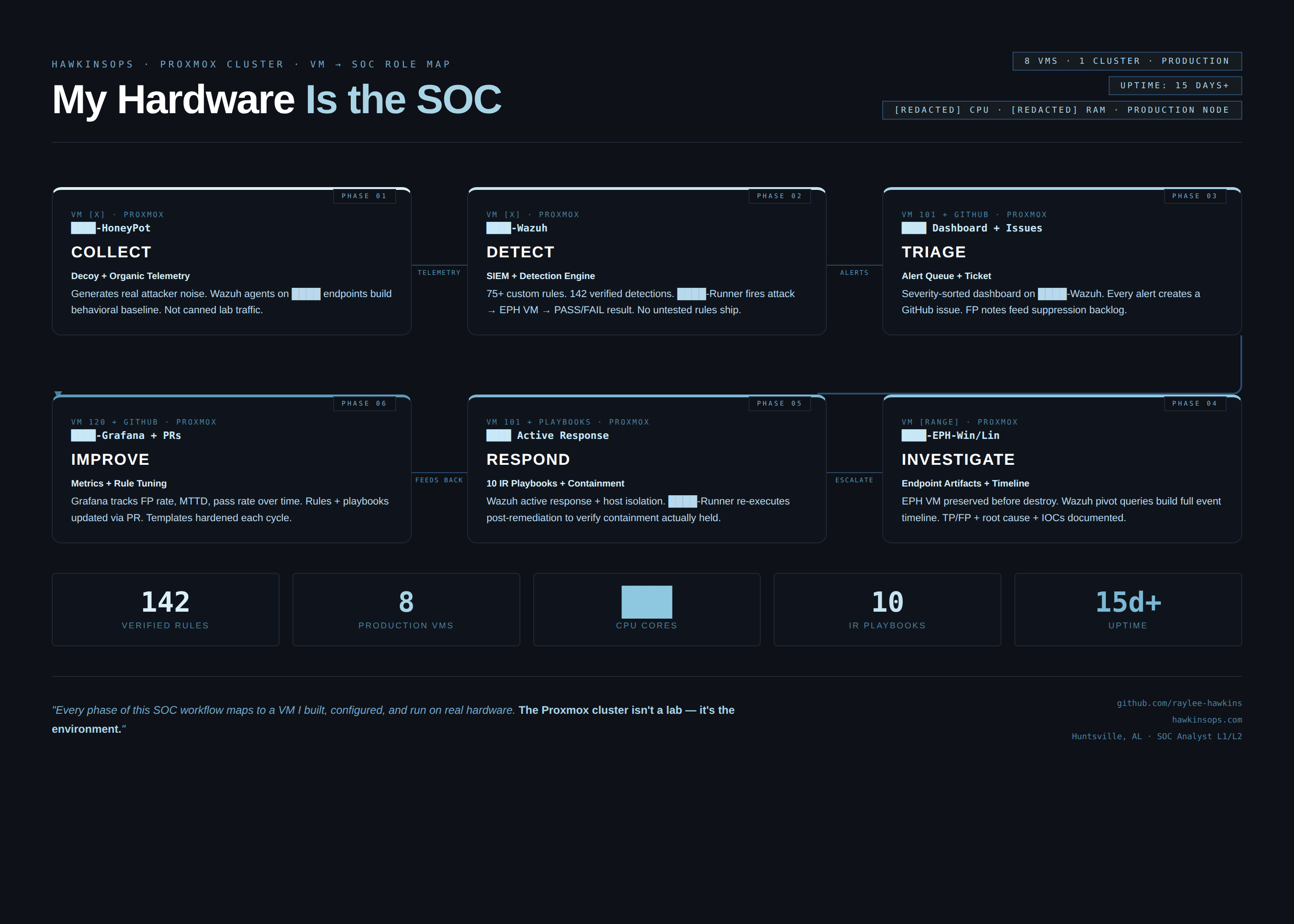
The HawkinsOperations detection library reached a verified baseline: 103 Sigma rules, 28 Wazuh rule blocks, and 79 Splunk detection searches across 9 SPL files — all confirmed by CI and reproducible from repo root. The gap was not rule correctness. It was workflow validity. None of those rules had been run against continuous live telemetry in a real environment with a real analyst decision loop on top. The question became: do these rules fire on actual endpoint and VM behavior, at SOC speed, in a way that produces actionable alerts rather than noise?
Problem
- Wazuh agent coverage across Windows 11 Enterprise endpoint and Proxmox-hosted VMs (7 agents active at time of case study).
- Agents stream telemetry (process creation, file integrity, authentication events, network connections) to a Wazuh manager.
- Detection rules deployed from
dist/wazuh/local_rules.xml- generated byscripts/build-wazuh-bundle.ps1from the verified rule set incontent/detection-rules/wazuh/rules/. - Splunk operates in the lab as an investigation layer with live Windows telemetry ingest and validated SPL pivots against real Event ID 4688 process-creation data.
Approach
- Observe Wazuh alert stream. Classify by rule level (low / medium / high / critical).
- Pivot on process trees and parent-child relationships for high-level alerts.
- Correlate with known-good baselines; apply suppression for confirmed noise patterns.
- For any critical or high alert: apply the documented SOC analyst decision flow - classify -> pivot -> validate source -> document findings or escalate suppression.
- Capture alert evidence artifacts per
PROOF_PACK/EVIDENCE_CHECKLIST.mdpolicy (redacted where internal identifiers are present).
Outcome
- 15,052 alerts observed in a single 24-hour monitoring window - confirming agent connectivity and rule coverage at scale.
- CVE-2025-55130 identified during active monitoring. Remediation steps applied and verified as closed.
- Agent health confirmed via Wazuh manager dashboard after each bundle redeploy cycle.
- Bundle rebuild verification command:
pwsh -File .\scripts\build-wazuh-bundle.ps1
Evidence
All artifacts from this project are collected in the repository evidence directory. Screenshots containing internal identifiers are redacted per repo sanitization policy.
- PP_SOC_Integration evidence directory (GitHub) - Wazuh alert screenshots, agent status, CVE remediation artifacts.
- Splunk VM 104 exports (GitHub) - sanitized live-ingest validation summary and validated Event ID 4688 SPL pivots.
- Full project package (GitHub) - README, docs, and structured proof artifacts.
- Upcoming project direction doc - next phase priorities and expansion plan.
Lessons + next hardening step
- Single-node Wazuh manager - home lab, not clustered. No high-availability or cross-site correlation.
- Splunk now has live Windows telemetry ingest with validated Event ID 4688 SPL pivots, but a full alert-to-investigation artifact is not packaged yet.
- 15,052 alerts/24h includes untuned noise - suppression tuning is ongoing work, not a completed deliverable.
- Screenshots contain internal hostnames and identifiers; all are redacted per
PROOF_PACK/EVIDENCE_CHECKLIST.md. - No correlation engine across data sources - ATT&CK lateral movement coverage relies on per-host telemetry only at this stage.
Next hardening step
- Package one full alert-to-investigation artifact so the investigation workflow is reviewer-verifiable end to end.
- Expand Proxmox VM coverage - add additional agent targets for lateral movement simulation.
- Build a daily alert triage log as a structured artifact (consistent format, reviewer-readable).
- Add synthetic event generators for Wazuh regression testing after rule changes.
- Publish a false-positive review matrix per rule family.